Learn how cybercriminals use brand jacking to harvest user credentials and propagate malware in a guide to Brand Hijacking Attacks.
A Step-by-Step Guide to Brand Hijacking Attacks
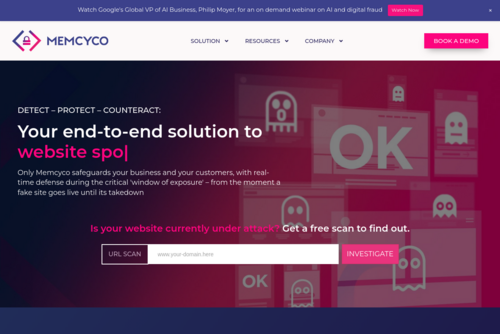
From https://www.memcyco.com 384 days ago
Subscribe
![]() “You are most welcome Gaurav....”
“You are most welcome Gaurav....”
![]() “transition plan is the first thing to start. Thank for sharing this...”
“transition plan is the first thing to start. Thank for sharing this...”
![]() “I have been using Picuki, and other tools. But, I was not aware about IG...”
“I have been using Picuki, and other tools. But, I was not aware about IG...”
![]() “I am not into Google Sites. I still and always prefer WordPress. Easy to...”
“I am not into Google Sites. I still and always prefer WordPress. Easy to...”
![]() “Semrush is changing. And, I am following the path....”
“Semrush is changing. And, I am following the path....”








Comments